Google is currently displaying a warning message in the search results of computers that are infected with the DNSChanger malware. They are doing this to help prevent 500,000 computers from going offline July 9, 2012. The DNSChanger malware is a trojan horse (malicious software) that changes your DNS (Domain Name Services) settings to redirect you to a malicious website.
Your DNS is responsible for translating a domain (onlinethreatalerts.com) into an IP address number so that a website can be located on the internet. The internet is made up IP addresses similar to your telephone system. Every website has an IP address number (192.168.5.1), just as how every telephone has a number (921-555-4586).
When you type www.onlinethreatalerts.com into your browser, it sends the domain name to your DNS, which searches for the name and returns the IP address. With the IP address, your browser can locate www.onlinethreatalerts.com on the internet. Without the DNS around the world, the internet would not work properly, unless you have the IP addresses of the websites that you are visiting. Just think about your cell phone contacts; it is easy to search for a name and call the person who you want to talk to. What if you didn't have your phone book; it would be difficult to find someone's phone number by just looking at numbers only.
If the DNSChanger malware changes your DNS settings, it means that you will be taken to a malicious website, when you type the name of a legit website in your browser.
Let us take your cellphone contacts as an example:
If someone goes into your cell phone book (contacts) and changes the phone numbers of your contacts, when you dial the contacts by name, you will be calling someone else, instead of the names of the persons that you have dialed. That is what the DNS changer trojan does to your computer DNS settings.
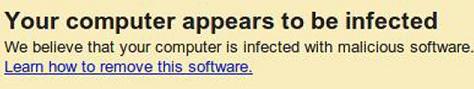
Google displaying a warning message in the search results, of a computer that is infected with the DNSChanger malware.
The FBI was able to arrest the persons behind this scam, but they are not able to remove the DNSChanger malware from the over half of a million computers infected.in order to prevent those computers from going offline, the FBI converted the DNS servers used by the scammers to a legitimate one. This was done to give the persons with the infected computers, sufficient time to remove the malware from their computers.
These converted DNS servers should have been taken down on March 9, 2012, but was postponed until July 9, 2012. If the malware from the infected computers is not removed, they will not be able to browse the internet on and after July 9, 2012.
You can use the following websites, to check if your computer is infected with the DNSChanger malware:
Use the following tools to remove the DNS Changer malware: