Hackers have found a clever way of gaining account to your social networking accounts and then using these accounts to send spam or malicious links to all of your friends. If you are taken to any website that requires you to press the following keyboard key combinations: CTRL + L, CTRL + C, CTRL + W and CTRL + V, please do not, this is a trick to gain access to your Twitter or Facebook account.
Hackers will trick you into using the keyboard combinations: CTRL + L, CTRL + C, CTRL + W and CTRL + V on a malicious website, to copy your account sign in authentication token, which they will use with the Twitter or Facebook API to post things to your account.
This is how the hackers gain access to your account
They will post or tweet a malicious link on your Facebook Timeline / Wall or in Twitter. You may also receive these links in an email message or on other social networking websites.
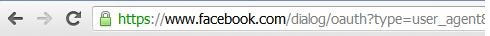
If you click on the link, you will prompt to grant access to your Twitter or Facebook account.

If you click "Okay" to grant access, a new web browser window will open and you will be instructed to press the keys: CTRL + L, CTRL + C, CTRL + W and CTRL + V, to watch or view some content.
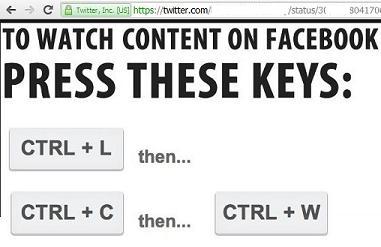
Pressing CTRL + L, selects the current website address or URL in your web browser's address bar. This is the sign in authentication token for your Facebook or Twitter account.
Pressing CTRL + C, copies the selected website address or URL (authentication token) in your web browser's address bar.
Pressing CTRL + W, closes the current web browser window.
Pressing CTRL + V, paste the website address or URL (authentication token) into the malicious web page created by the hackers.
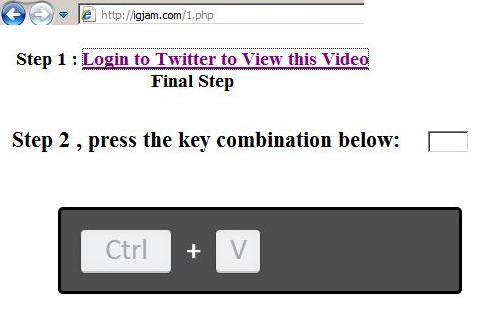
With the authentication token and the Facebook/Twitter API, the hackers will be able to post or tweet anything to your Facebook or Twitter account.
If you were tricked into pressing the keys CTRL + L, CTRL + C, CTRL + W and CTRL + V on a website, please change your Facebook or Twitter password.
Also, if you have noticed that things are being posted to your friends, appearing as if they came from you, please change your password.