Cyber-criminals are sending out the fake Department of Transport (DoT) email message below with subject: "DoT Payment Receipt," with a malicious Microsoft Excel document("PaymentReceipt.xls") attached, disguised as an invoice or receipt. The malicious attachment contains a Macro, which is a set of instructions that is used in Microsoft Office to automate different tasks. If the malicious Microsoft Excel attachment is opened and the recipients enable "Macro" or "Enable Content," the set of Macro instructions will attempt to download a Trojan horse from a remote computer server and infect the recipients’ computers.
The Trojan horse will then be used by the cyber-criminals to steal the infected computer users' banking, social media, PayPal and other credentials.The Trojan horse can also be used to steal the victims’ financial information and other sensitive information without their knowledge.
Please note that the Trojan horse will only infect computers running the Microsoft Windows operating system.users of the Mac, IPhone, IPad, Blackberry, Windows phone or Android phone are not affected.
Although the fake and malicious email message appears as if it was sent by Department of Transport (DoT), it was not. The cyber-criminals responsible for the emails, spoofed the email message to make it appear as if came from Department of Transport (DoT), to make it look legitimate. So, there is no need to contact Department of Transport. Cyber-criminals spoofed email addresses to trick their victims into opening malicious attachments or clicking malicious links, thinking the fake email message was sent from a legitimate company.
Remember, never enable Macro or “Enable Content” for a Microsoft Word, Excel or other Microsoft Office documents, regardless of where the email message came from.
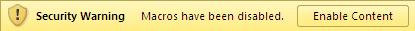
Macro was created to automate tasks in Microsoft Office, but cyber-criminals started abusing this useful tool over a decade ago, by using it to download and infect their victims’ computers with viruses, Trojan horse and other malware. That is why Microsoft decided to disable Macro by default and gave Microsoft Office users the option of enabling or disabling it.
The Fake and Malicious DoT Email Message
Subject: DoT Payment Receipt
[Automated message. Do not reply]
Thank you for your payment. It is important that you print this receipt and record the receipt number as proof of your payment. You may be asked to provide your receipt details should you have an enquiry regarding this payment.
Now, persons who were tricked into opening the malicious Microsoft Excel document and enabling Macro or “Enable Content,” should do a full scan of their computers with the antivirus installed on them.