Online users, be aware of CPU-Hijacking Bitcoin Miner applications. Also known as "Application.BitCoinMiner" to antivirus software makers, it is an application or program that uses the computer's physical resources (memory, processing power, etc) to generate units of a virtual or digital cryptocurrency. It can make your PC or mobile device run slower than usual. When it is activated the infected device's CPU load goes up to 100%, which slows down everything else because all the CPU processing power is used up. In other words, the malicious applications will slow down your computer or mobile device to a crawl. This makes it impossible for the infected device to function properly and will drain the battery very quickly because of the high CPU usage.
A CPU-Hijacking Bitcoin Miner called BlackWhats
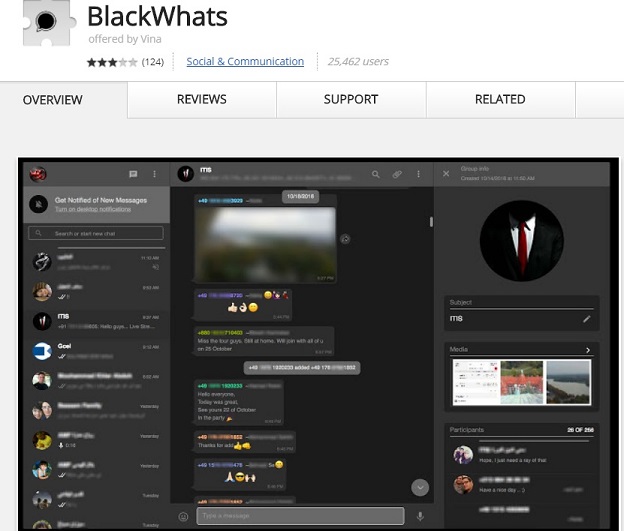
Black Theme for Whatsapp Web - BlackWhats - Black theme for Whatsapp Web ™
CPU-Hijacking Bitcoin Miner applications may also do the following:
- Displaying pop-up ads.
- Hijacking your browser.
- Inserting ads into the web pages, redirect your browser search, collect your personal information and sell it for advertising.
Here is a list of CPU-Hijacking Bitcoin Miner applications by the names given to them by antivirus software makers:
- Application.BitCoinMiner.UB
- Tool.BtcMine.1100
- PUA.JScoinminer
- BitCoinMiner,
- Application.BitCoinMiner.SX
- JS:Application.BitCoinMiner.TW
- Application.BitCoinMiner.[variant],
- JS:Application.BitCoinMiner.[variant]
- BITCOINMINER.SX
About cryptocurrency
A cryptocurrency is an anonymous, decentralized form of digital currency, which can be used online as a medium of exchange much like traditional, physical currencies. Multiple cryptocurrencies exist, such as BitCoin, Ethereum, and Monero.
The 'crypto' part of the term refers to the use of cryptography both for creating the currency units and for securing transactions made with the units. Because of the anonymity provided by cryptocurrency, its legality and acceptance varies considerably between countries.
About cryptocurrency mining
Cryptocurrency units can be created by any user with specialized mining programs or miners that run the mathematical calculations needed to generate a unit of a particular cryptocurrency.
Because the calculations are complex, many enthusiasts will build computers with specialized hardware and software to handle the work. Some websites also support cloud mining, where users visiting the site essentially allow temporary use of their computer's processing power to perform part of the calculating work, usually in exchange for a service offered by the site.
Some malware includes miners as part of their payload; in such cases, the malware is hijacking a user's computer to create cryptocurrency units for the malware author's benefit.
Most antivirus software are able to remove most malicious CPU-Hijacking Bitcoin Miner, therefore, victims of these applications should scan their computers or mobile devices with the antivirus software installed on them.