Cyber-criminals are using an old technique in an attempt to infect their potential victims’ computers with viruses, Trojan horse or other malware. The technique involves sending their potential victims a fake email message with a malicious or dangerous Microsoft Word or Excel document attached. The malicious document contains a set of malicious code or instructions called a Macro, which when enabled, will download and infect the victims’ computers with viruses, Trojan horse or other malware. So, only trusted Microsoft Office documents with Macros should be open.
A few years ago Microsoft disabled Macro in Microsoft Office by default because of Macro viruses. Macro is a very powerful and productive tool for Microsoft Office because it helps users automate simple and complex tasks in Microsoft Office. But, this productive tool was misused by cyber-criminals, who realized that they could use it to download and infect their victims' computers with malware. So, due to this threat, Microsoft disabled Macro in Microsoft Office by default and gave users the ability to enable it, if the document that they are opening is a trusted one.
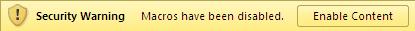
Microsoft Word or Excel Prompting a User to enable Macro via “Enable Content” or "Enable Editing"
How to Protect Yourself
If you are sent an unexpected email message with an attached Microsoft Word or Excel document, ask to open the document, and then ask to "Enable Content" or "Enable Editing" in order to view the content, please delete the document. Enabling Macro via "Enable Content" will run or execute the malicious code or Macro, which will download and install Trojan horse, viruses or other malware on your computer.
Once your computer has become infected, especially with a Trojan horse, the cybercriminals behind the email message will be able to access and take control of your computer remotely from anywhere around the world. They may spy on you, use your computer to commit cybercrimes, or steal your personal and financial information.
Please note that Macro viruses also affect Microsoft Powerpoint.
If you were tricked into opening a malicious Microsoft Word or Excel document and enabling Macro or "Content", we recommend doing a full scan of your computer with the antivirus software installed on it. If you don’t have antivirus software installed on your computer, please click here for a list of free antivirus software.
Click here for a list of email attachments you should never open, regardless of where they came from.
For a list of virus email messages, please click here.