There is a new and more dangerous ransomware or malicious computer program called Petya that is infecting computers, ATMs and other devices around the world running Microsoft Windows. Petya is being spread via fake email messages with a malicious Microsoft Office (Word, Excel) document or a Zip file attached. Once the malicious attachment is opened, the Petya ransomware will start spreading to other computers running Microsoft Windows on the same network.
Once a computer is infected, the ransomware will encrypt the files on it or make them unreadable, reboots it, and encrypts the MFT (Master File Tree) tables for NTFS partitions, which prevents victims from booting or accessing their computers. It also overwrites the MBR (Master Boot Record) with a custom bootloader that shows the ransom note below.
The Petya Ransom Note or Message
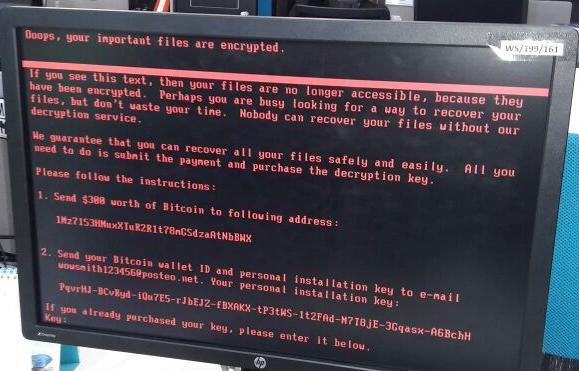
The Petya ransomware uses the following email address wowsmith123456@posteo.net for contact purposes and asks for a payment of $300 in Bitcoin for the victims to receive the key necessary to decrypt or make their files readable again. Because of this, Petya is more dangerous and intrusive compared to other versions or strains because it reboots systems and prevents them from working.
How to Protect Yourself Against the Petya Ransomware
Cyber criminals or hackers flood mailboxes with spam thus sending out fake email messages with malicious documents that deliver ransomware. This attack relies on users opening attached malicious document that will appear legitimate. Therefore, it is important that recipients of unexpected email messages never open the attachments in them, or have their I.T department or a tech-savvy family member or friend check the attachments before they attempt to open them.
Also, it is important that computer users and network administrators backup their important files in case they need to restore them if their computers get infected.
Petya spread via Server Message Block (SMB), a network protocol mainly used for providing shared access to files, printers, and serial ports and miscellaneous communications on a network.