The email message below with the subject: "Email Security Reset", is a phishing email designed to steal your user name and password. The email indicates that the recipient's email server was upgraded and he/she needs to do a password reset. The email contains a link to the website buysellleasetrade.com, if clicked on, will take you to the web page "webmail_reset.htm", where you will asked to enter your user name and password.
A Copy of the Security Reset Phishing Email Scam
From: E-mail Administrator [mailto:upgrade@service.administrator.com]
Sent: Friday, June 21, 2013 11:27 AM
Subject: Email Security Reset
This is the webmail administrator.
Please, be informed that the email server has just been upgraded and your email needs reset immediately through the Email Administrator's page.
This process is to keep your email functions updated and protected as always.
Click here to reset your email now - hxxp://buysellleasetrade.com/phpform/ webmail_administrator_password_reset/webmail_reset.htm
Regards,
Email Administrator.
This is how the phishing web page "webmail_reset.htm" looks on buysellleasetrade.com
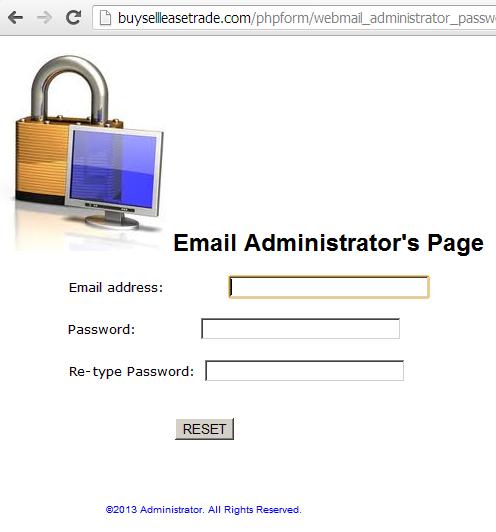
Do not enter your user name and password on this web page. If you do so, you will only be sending it to the scammers behind this phishing web page.
The buysellleasetrade.com has nothing to do with you webmail, so ask yourself, why should I go to this website to reset my webmail password? If you stop and think about it, you will realize this is a phishing scam. Also, server upgrades or maintenance do not require a password change or reset. And, if you were tricked into entering your user name and password by this phishing email, please change that password right now!